Healthcare Cybersecurity 2026: The CFO's Financial Risk and Budget Planning Guide
Ransomware doesn't just threaten patient data. It threatens your operating budget, your vendor contracts, and your organization's survival.
The Stryker cyberattack in March 2026 put hospital CIOs on high alert globally. But for many healthcare finance leaders, the real question isn't whether IT is patching vulnerabilities. It's whether the organization has modeled the financial exposure, structured vendor contracts to limit liability, and reserved the capital to survive 24 days of operational downtime.
Cybersecurity is no longer an IT department problem. It is a balance sheet problem.
Why Finance Leaders Are Now on the Front Line
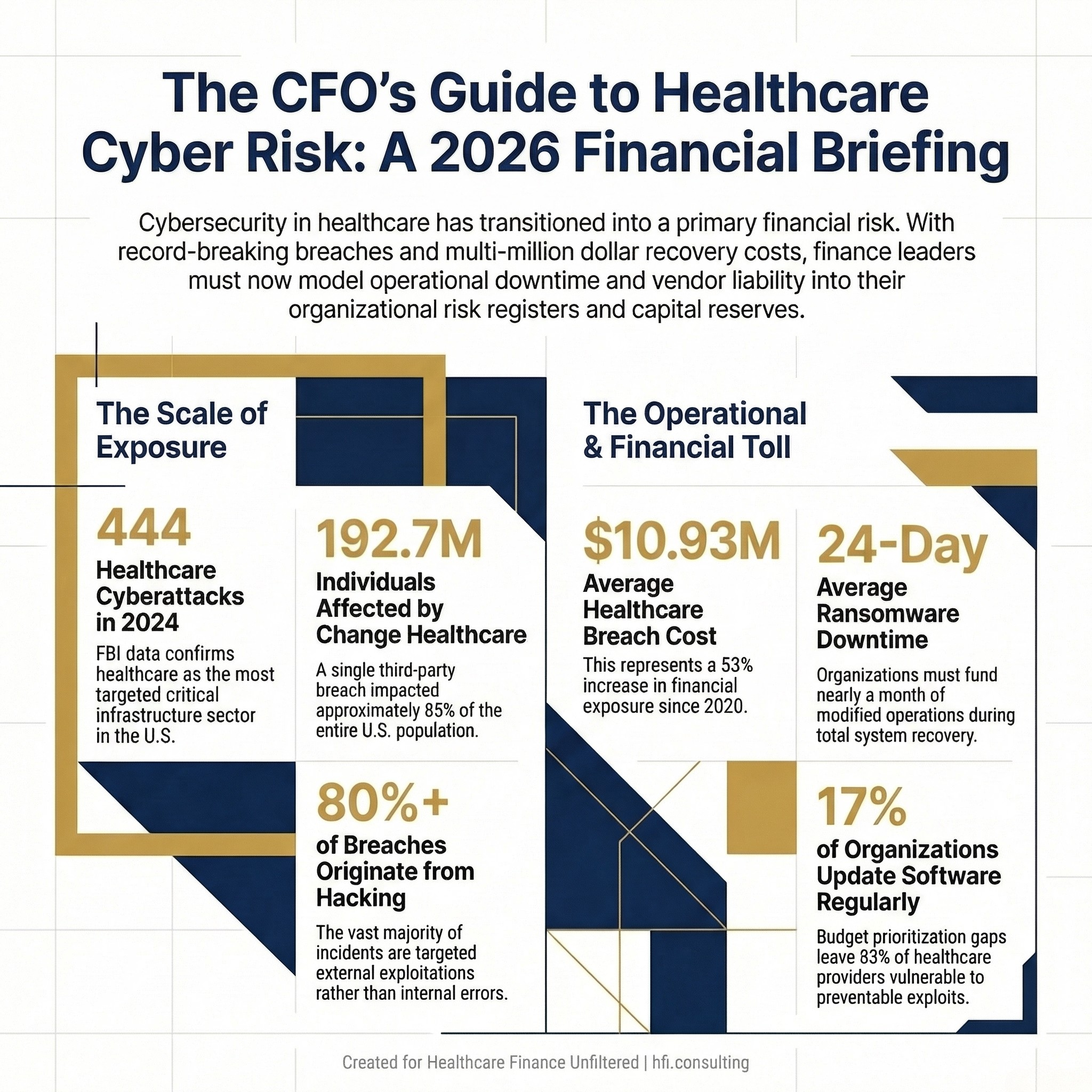
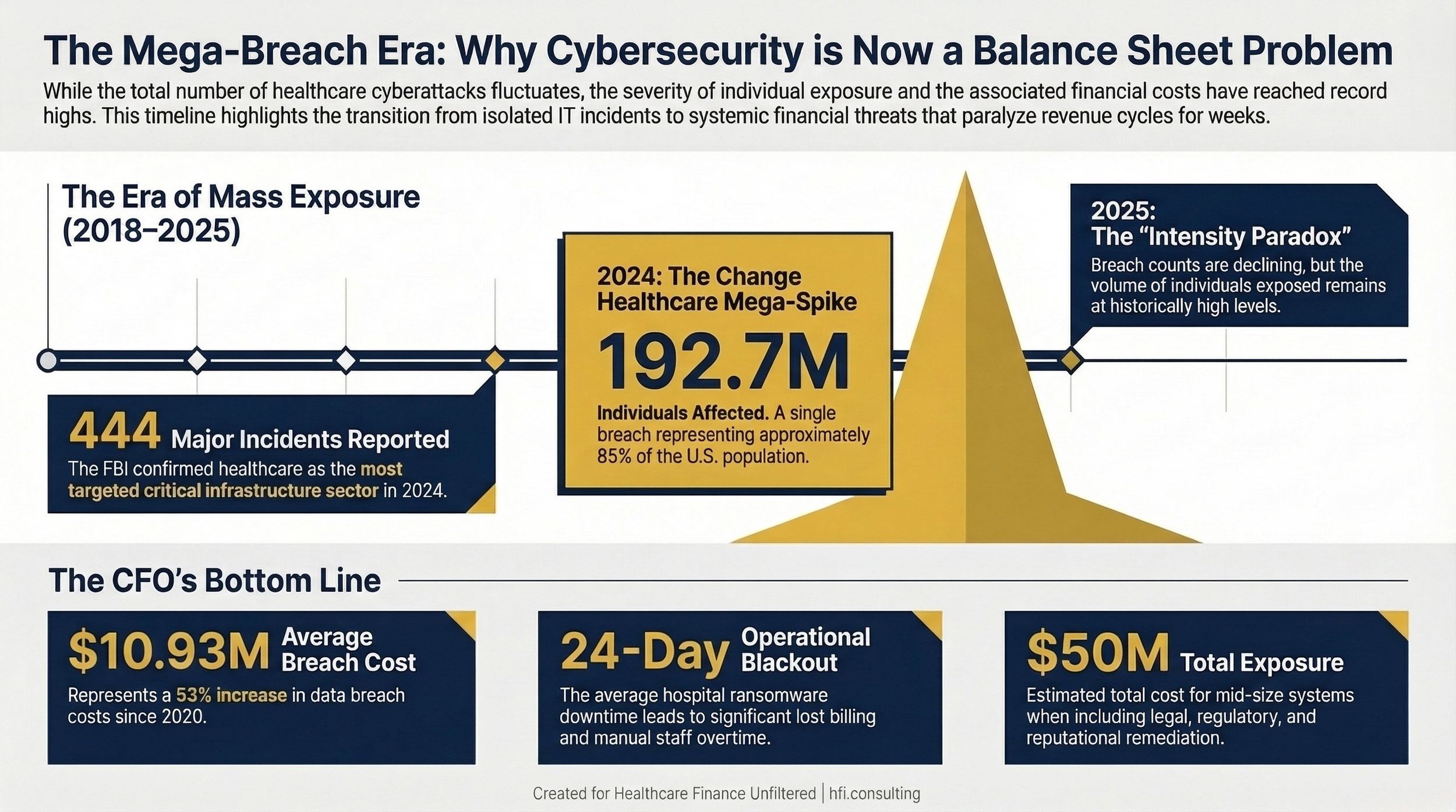
Healthcare is the most targeted critical infrastructure sector in the United States for cybercrime. The FBI's 2024 Internet Crime Report confirmed 444 reported incidents against healthcare organizations, comprising 238 ransomware threats and 206 data breach incidents. No other sector matched that combined total.
The financial consequences are equally stark. The average cost of a healthcare data breach reached $10.93 million in 2023, a 53% increase from 2020. When you add the operational cost of downtime, legal defense, regulatory fines, and reputational remediation, the true exposure for a mid-size health system can exceed $50 million for a single incident.
That number belongs in your risk register, not just your IT department's incident log.
The Change Healthcare ransomware attack in 2024 affected an estimated 192.7 million individuals. For context, that represents approximately 85% of the U.S. population. The attack disabled billing and claims processing for thousands of hospitals and physician practices, creating a cascading cash flow crisis that lasted months. Ascension Health, which I know well from my time managing financial operations across seven of its hospitals, was also breached in 2024, with 5.4 million patient records compromised.
These are not anomalies. They are the new operating environment.
Year-by-year healthcare data breach count and individuals affected (2018–2025), with Change Healthcare 2024 mega-spike labeled.
The Vendor Risk Problem Nobody in Finance Is Solving
Here is the number that should concern every CFO more than any other in your cybersecurity briefing: the majority of large healthcare data breaches originate at business associates and third-party vendors, not at the hospital or health plan itself.
In 2023 and 2024, business associates accounted for a disproportionate share of mega-breaches. The MOVEit Transfer vulnerability alone was exploited across multiple healthcare vendors simultaneously, exposing millions of records through a single third-party file transfer tool. Change Healthcare, a clearinghouse, not a direct care provider, became the single largest healthcare data breach in history.
The 21st Century Cures Act requirements for interoperability have expanded the attack surface significantly. Every connection point between your EHR and an external platform is a potential entry vector. And if your vendor has weak security posture, your organization bears the HIPAA notification and regulatory exposure regardless of where the breach occurred.
From the payer side at Florida Blue Medicare, I watched how third-party data flows multiply risk in ways that internal IT audits rarely capture. A vendor handling claims data, authorization workflows, or encounter submissions holds PHI that is just as regulated as anything on your internal servers. But vendors are often evaluated on implementation timelines and pricing, not on cybersecurity maturity scores.
Finance leaders need to change that calculus.
What Finance Leaders Should Be Negotiating Into Vendor Contracts
This is where finance can have direct operational impact before an attack ever occurs.
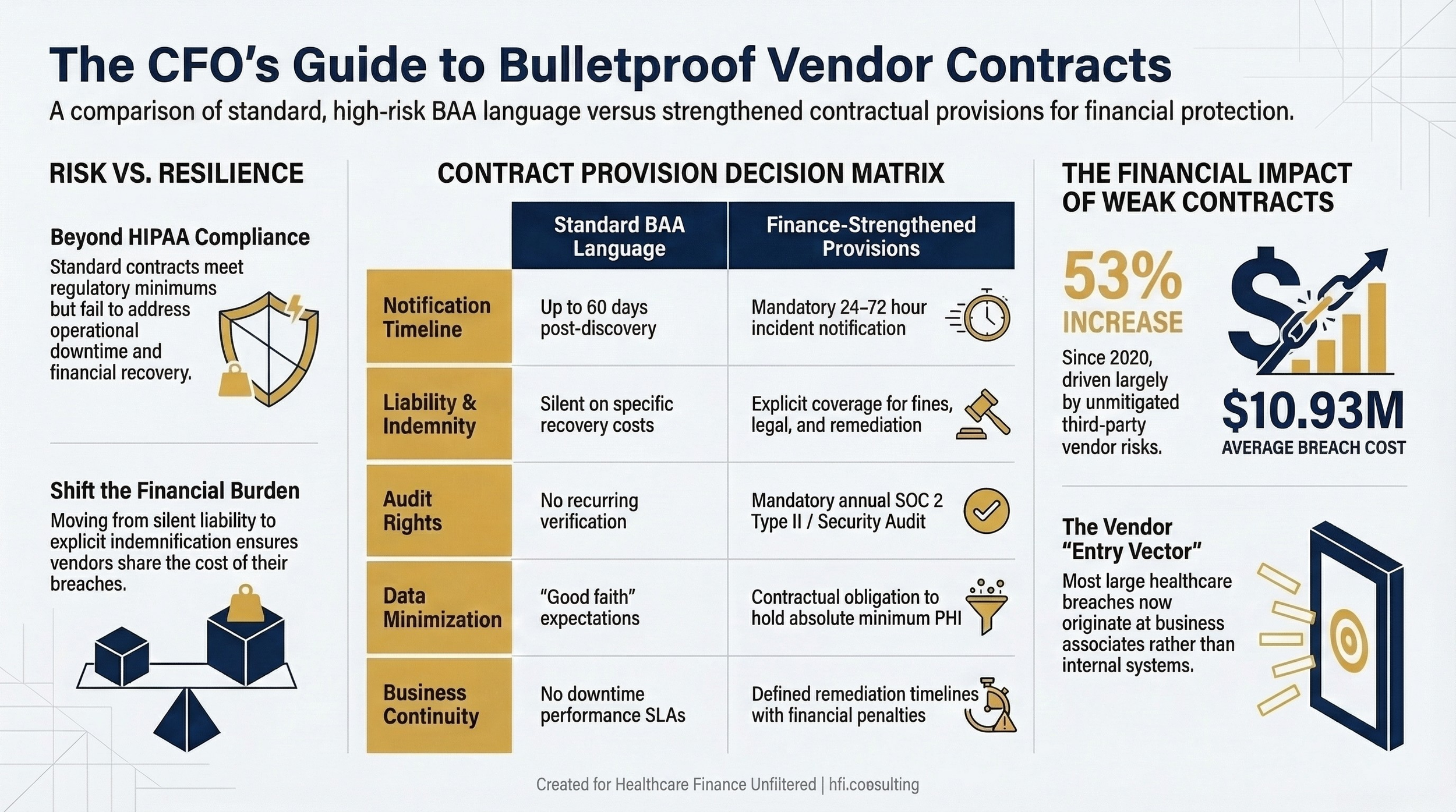
Every Business Associate Agreement (BAA) your organization signs is a legal document, but it is also a financial risk document. Standard BAA language often falls short of addressing what actually happens when a vendor breach exposes your patient data.
At a minimum, every vendor contract involving PHI access should include:
Incident notification timelines. HIPAA requires notification within 60 days of breach discovery. Your contract should require vendor notification to your organization within 24 to 72 hours of an incident, not 60 days.
Liability and indemnification provisions. If a vendor breach triggers OCR investigation, class action litigation, or patient notification costs against your organization, the vendor's indemnification obligations should be clearly defined. Many standard agreements are silent on this.
Cybersecurity audit rights. Your contract should give your organization the right to request a SOC 2 Type II report or equivalent security certification at least annually. Requiring this in the contract creates an accountability mechanism.
Data minimization requirements. Vendors should only hold the minimum PHI necessary for the contracted service. This limits exposure if they are breached. Include this as a contractual obligation, not just a good faith expectation.
Business continuity provisions. If a vendor experiences a cyberattack and cannot perform contracted services, what is the downtime SLA? What is the remediation timeline commitment? What financial penalties apply? The Change Healthcare situation revealed how few contracts addressed this scenario.
Two-column table: "Standard BAA Language" vs. "Finance-Strengthened Contract Provisions" covering notification timelines, liability, audit rights, data minimization, and business continuity
Building the Cyber Incident Financial Reserve
Most healthcare finance leaders have capital reserves for facility repairs, equipment replacement, and unexpected regulatory settlements. Very few have built a dedicated cyber incident reserve, even though the probability of a significant incident now rivals many of the scenarios those reserves were designed to address.
The financial modeling for a cyber reserve should account for four distinct cost buckets.
Immediate operational costs. The average hospital ransomware downtime in 2022 was 24 days, at an average cost of $10 million. This includes staff overtime for manual processes, temporary technology resources, lost billing capacity, and patient diversion. Your reserve should be able to fund at least 30 days of modified operations.
Regulatory and legal costs. OCR imposed 21 financial penalties in 2025. The settlement amounts ranged from $5,000 to $3 million for individual incidents, with larger penalties reaching into the tens of millions for systemic failures. State attorneys general are increasingly active as well; the California AG imposed a $49 million settlement on Kaiser Permanente in 2023. Legal defense costs alone for a mid-size system can reach $2 to $5 million before any settlement is reached.
Notification and remediation costs. HIPAA requires individual breach notification, which for large breaches involves printing, mailing, credit monitoring services, and call center support. For a breach affecting 100,000 individuals, this can run $1 to $3 million depending on notification method and scope.
Cyber insurance gap analysis. Most healthcare cyber insurance policies carry exclusions, sublimits, and coinsurance requirements that leave material gaps. Finance leaders should work with their risk management team annually to model the gap between policy coverage and realistic total exposure. The gap is almost always larger than leadership expects.
The Budget Conversation Your CISO Is Afraid to Have
A Ponemon Institute survey found that only 17% of healthcare delivery organizations update software on a regular basis, and only 20% educate employees about ransomware risks. Additionally, 85% of healthcare organizations run on legacy network infrastructure that predates modern cybersecurity architecture.
These are not failures of will. They are failures of budget prioritization.
The CFO controls the budget conversation. That makes cybersecurity investment, or the lack of it, a finance decision as much as an IT decision.
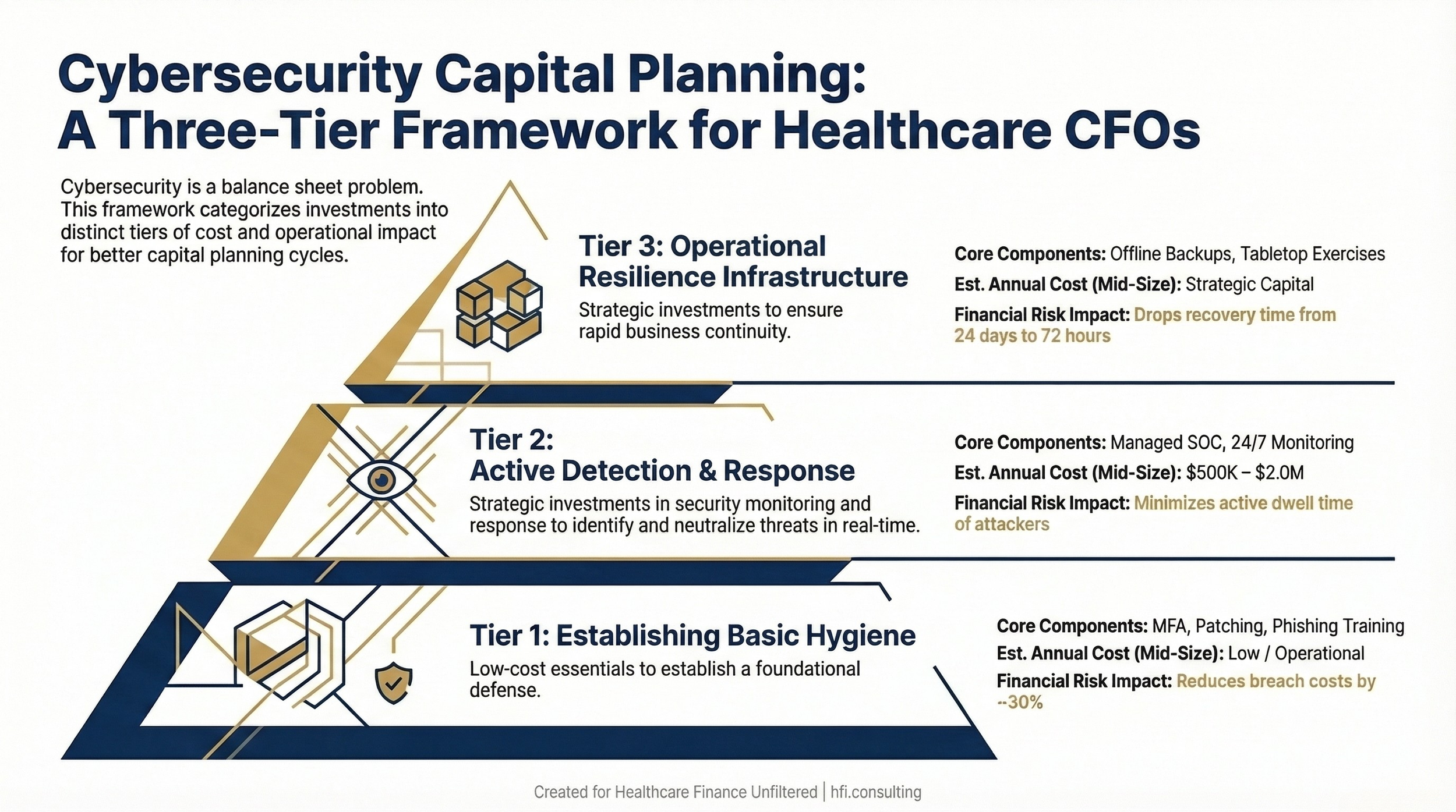
The practical framework for the budget conversation involves mapping cybersecurity spend against three tiers of risk mitigation.
Tier one: Basic hygiene. Multi-factor authentication, endpoint protection, patch management, and annual staff phishing simulation training. These address the majority of initial access vectors at relatively low cost. A Ponemon study found that organizations with mature basic hygiene reduce average breach costs by approximately 30%.
Tier two: Detection and response. A managed security operations capability that provides 24/7 monitoring and incident response. For most community hospitals and regional health systems, a managed SOC is more cost-effective than an internal team. Annual cost for a mid-size organization typically runs $500,000 to $2 million depending on scope.
Tier three: Resilience infrastructure. Offline, immutable backups. Tested downtime procedures. Cyber incident tabletop exercises conducted at least annually with clinical and finance leadership, not just IT. This tier is where the difference between a 24-day recovery and a 72-hour recovery gets made.
The return on investment for cybersecurity spend is genuinely difficult to calculate, because you are measuring loss prevention rather than revenue generation. But the inverse is calculable: a $10 million breach cost, weighted by the probability of occurrence, quantifies the expected annual loss that prevention spending is offsetting.
Stacked pyramid or three-column layout showing Tier 1 (Basic Hygiene), Tier 2 (Detection and Response), and Tier 3 (Resilience Infrastructure) with estimated cost ranges and risk mitigation impact for each tier.
OCR Enforcement: The Financial Exposure Finance Leaders Are Underestimating
The HHS Office for Civil Rights is not resourced for comprehensive enforcement. Its budget has remained flat since 2009 while its caseload has grown dramatically. There is currently a growing backlog of investigations.
But OCR has adapted by focusing its enforcement on the HIPAA Security Rule's risk analysis provision, which is the most commonly identified violation. Every hacking incident OCR investigates now triggers a risk analysis review. If your organization cannot demonstrate that it conducted a comprehensive risk analysis, identified gaps, and implemented a risk management plan, you are exposed to civil monetary penalties regardless of whether the breach was caused by a sophisticated nation-state actor.
As of January 2026, OCR has closed 11 investigations of hacking incidents with financial penalties specifically for risk analysis failures under its focused enforcement initiative.
This is a compliance obligation that finance leaders can verify and fund. A formal HIPAA risk analysis, conducted by a qualified third party, typically costs between $50,000 and $200,000 depending on organizational complexity. That investment provides documented evidence of compliance posture and substantially reduces regulatory exposure in the event of a breach.
State attorney general actions are an additional layer of financial risk. In 2024, the New York AG imposed $1 million in penalties on Albany ENT and Allergy Specialists, plus a $2.25 million mandated cybersecurity investment. California's AG imposed $49 million on Kaiser Permanente. These actions often occur in parallel with OCR investigations, compounding the financial exposure.
If you are building a cybersecurity budget case for your board or assessing your vendor contract gaps, I have put together a Cyber Financial Risk Assessment Template that maps these cost buckets against your organization's current posture. Download it at hfi.consulting or reply to this email and I'll send it directly.
What Finance Leaders Can Do in the Next 30 Days
The impulse after reading a cybersecurity threat briefing is either to forward it to IT and consider the obligation discharged, or to request a comprehensive security audit that will take six months to scope. Neither response addresses your immediate financial exposure.
Here is a practical 30-day action framework for finance leaders.
Week one: Contract audit. Pull your top 20 vendor contracts involving PHI access. Evaluate each against the five contract provisions described above. Flag the gaps and bring them to your next vendor management conversation.
Week two: Insurance gap analysis. Request a side-by-side comparison of your current cyber insurance policy coverage against a realistic breach scenario model. Have your risk manager walk through the exclusions, sublimits, and coinsurance requirements.
Week three: Reserve assessment. Ask your treasury or budget team to calculate what 30 days of modified operations would cost under three scenarios: partial operational disruption, complete EHR downtime, and complete revenue cycle disruption. Compare that number to any existing cyber incident reserve.
Week four: Tabletop exercise request. If your organization has not conducted a cyber incident tabletop exercise with finance and operational leadership in the past 12 months, request one be scheduled. Ensure the scenario includes the revenue cycle and billing disruption, not just the clinical response.
None of these actions require a large budget authorization. They require finance leadership to treat cybersecurity as the operational and financial risk it demonstrably is.
The Downtime Procedures Your Revenue Cycle Team May Not Have
One of the most underappreciated financial risks in a ransomware event is revenue cycle disruption. Billing systems, clearinghouses, and authorization workflows are among the first systems affected when a health system goes into downtime mode.
Organizations that recover fastest from cyber events share a common characteristic: they had documented, practiced downtime procedures for every revenue-generating workflow before the attack occurred. That means paper-based claim submission pathways, manual authorization processes, and pre-established relationships with alternate clearinghouses if a primary vendor like Change Healthcare is compromised.
Building those procedures is a revenue cycle management investment. But the decision to fund it is a finance decision.
The organizations that waited to build downtime procedures until they were mid-attack in 2024 learned an expensive lesson that is now available to everyone else for the cost of implementation.
The Payer Perspective on Vendor Cybersecurity Risk
From the payer side at Florida Blue Medicare, the cyber risk calculus looks somewhat different than on the provider side, but the vendor risk problem is identical. Payer organizations rely on an ecosystem of delegated vendors: PBMs, behavioral health carve-outs, data analytics platforms, and population health management tools. Each one holds member data. Each one has signed a BAA. Each one represents a potential breach pathway.
The financial exposure on the payer side includes regulatory penalties from CMS for Medicare Advantage plans, state insurance department actions, and member notification costs that can reach into the millions for a large plan. The reputational impact on plan selection is harder to quantify but equally real.
The 2024 Kaiser Foundation Health Plan breach affected 13.4 million individuals and resulted in a $49 million state AG settlement. For a Medicare Advantage plan operating on 2% to 3% margins, that is a material financial event.
Whether you are on the provider or payer side, the vendor risk framework is the same. The contract provisions matter. The monitoring matters. The insurance coverage matters. The reserves matter.
The Bottom Line for Healthcare Finance Leaders
The cybersecurity threat environment in 2026 is materially different from three years ago. Nation-state affiliated ransomware groups are operating with greater sophistication and are specifically targeting healthcare infrastructure. The Stryker attack and ongoing alerts from the FBI and AHA confirm that healthcare remains the highest-priority target.
Finance leaders who treat this as a technology problem are carrying unquantified balance sheet risk. Finance leaders who treat it as a financial risk management problem can take concrete, budgeted action in the next 30 days.
The organizations that will come through the next major cyber event in the best financial shape are not necessarily the ones with the most sophisticated technology. They are the ones that modeled the exposure, funded the reserves, tightened the vendor contracts, and practiced the response before it was needed.
That work starts with the CFO deciding it is their problem to own.
What is your organization's current approach to cyber incident financial reserves? I am working on a follow-up piece on cyber insurance gap analysis specifically for health systems and MA plans, and I would love to hear where finance leaders are finding the most significant coverage gaps. Hit reply and tell me what you are seeing.
P.S. Has your organization conducted a cyber incident tabletop exercise that included finance and revenue cycle leadership in the last 12 months? I am genuinely curious whether this is common practice or still an IT-only exercise. Reply and let me know.