Aetna $117.7M False Claims Act Settlement 2026: Risk Adjustment Compliance Guide for Payer CFOs
What Aetna's settlement reveals about chart review risk and the audit protocols your compliance team needs before DOJ comes knocking.
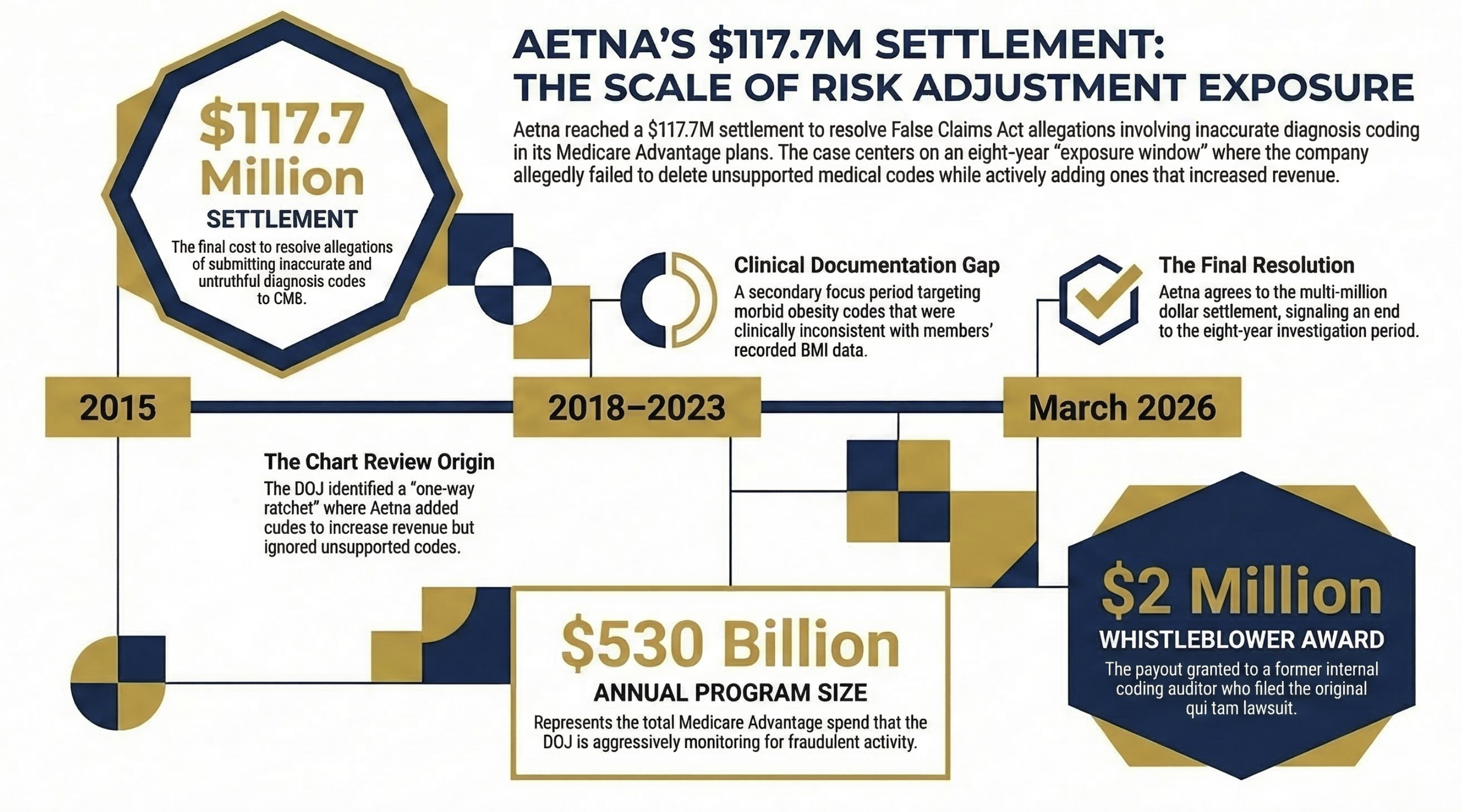
Aetna just agreed to pay $117.7 million to resolve False Claims Act allegations tied to inaccurate diagnosis coding in its Medicare Advantage plans — and the settlement details are a roadmap of exactly how DOJ investigators build these cases. The allegations span payment years 2015 through 2023, which means eight years of exposure existed before resolution. If your organization runs chart review programs or relies on vendor coders to submit diagnosis data to CMS, today's news is not a spectator event.
Horizontal timeline showing Aetna's exposure window (2015–2023), with three callout boxes: (1) $117.7M settlement, (2) $530B annual MA program size, (3) $2M whistleblower award.
The Settlement Details Every Payer Finance Leader Needs to Understand
On March 11, 2026, the Department of Justice announced that Aetna Inc. — the health insurer subsidiary of CVS Health — agreed to pay $117.7 million to resolve allegations that it violated the False Claims Act. The core allegation: Aetna submitted inaccurate and untruthful diagnosis codes for its Medicare Advantage enrollees to inflate risk adjustment payments from CMS.
This was not a single billing error. The DOJ's allegations describe a structural problem embedded in how Aetna managed its chart review program across multiple payment years. That distinction matters for every payer finance leader reading this.
The settlement resolves two distinct sets of allegations. The first covers payment year 2015 and Aetna's chart review program. The second covers payment years 2018 through 2023 and specifically targets morbid obesity coding. Neither violation was hidden from Aetna's own internal processes — which is the part that should concern your compliance team most.
How the Chart Review Program Became the Problem
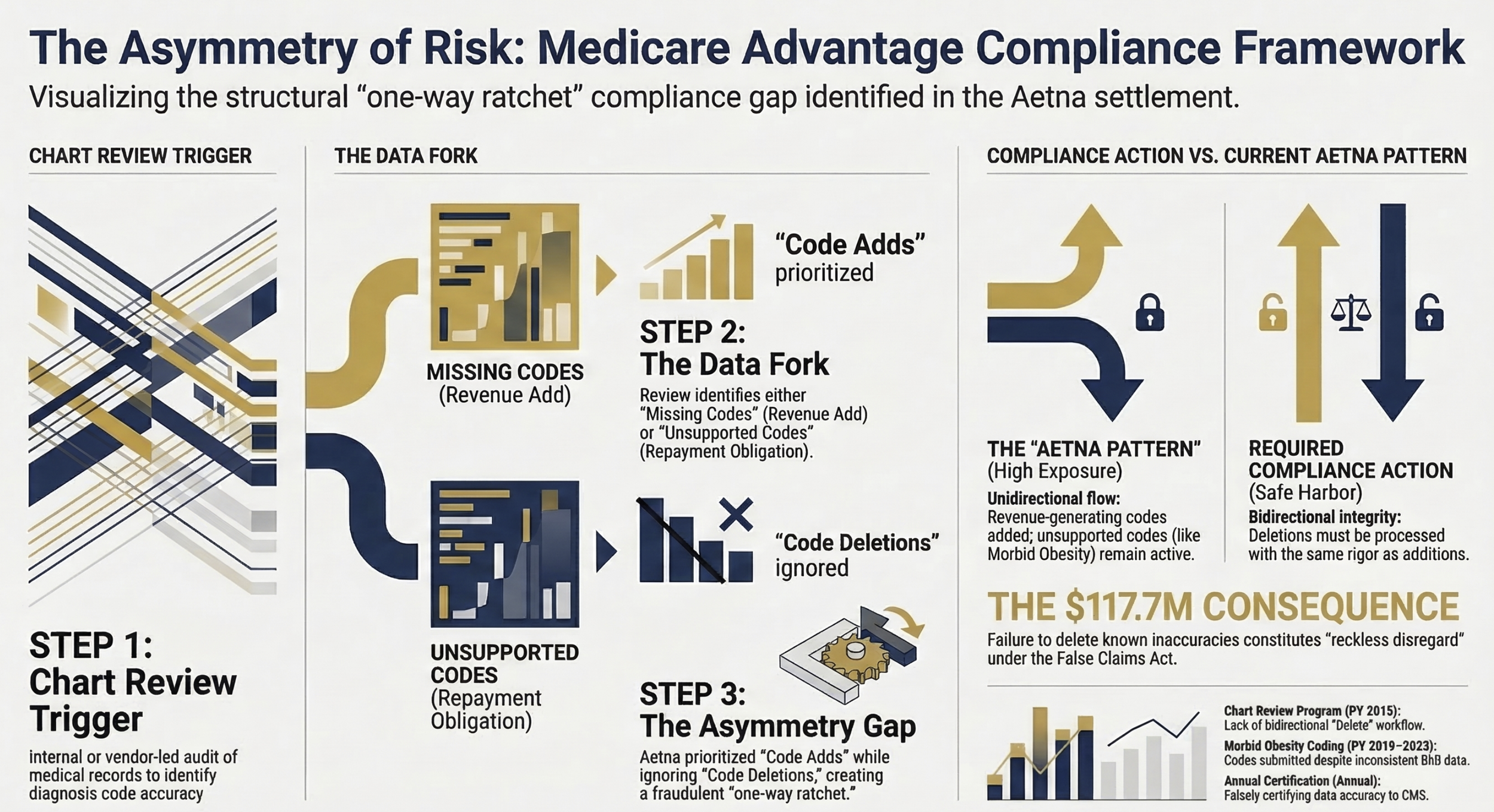
CMS pays Medicare Advantage Organizations a fixed monthly capitation rate, adjusted upward for sicker beneficiaries based on the diagnosis codes submitted by the plan. In theory, chart reviews are a legitimate and necessary tool. A plan reviews medical records, identifies documented conditions the original coder may have missed, and submits additional codes. Done correctly, this is accurate risk capture. Done incorrectly, it becomes the mechanism for a False Claims Act violation.
The DOJ's allegation against Aetna describes a one-way ratchet. Aetna's chart review program identified instances where it could submit additional codes and receive higher payments. But when those same chart reviews revealed that previously submitted codes were not substantiated — codes that, if deleted, would have required Aetna to reimburse CMS — Aetna did not delete them.
Submitting codes to add revenue: yes. Deleting codes to repay overpayments: no.
That asymmetry is what the DOJ characterized as fraudulent. And it is exactly the pattern that CMS has trained its auditors and the OIG's investigative staff to identify.
The Morbid Obesity Problem (2018–2023)
The second set of allegations is more operationally specific and, frankly, easier to build a case around. For payment years 2018 through 2023, the DOJ contends that Aetna submitted or failed to delete diagnosis codes for morbid obesity for members whose recorded Body Mass Index was inconsistent with that diagnosis.
Medical records for members diagnosed as morbidly obese typically include BMI recordings. When the recorded BMI does not support the diagnosis, the code is inaccurate. Aetna allegedly continued submitting these codes — or failed to delete them when the inaccuracy was apparent — resulting in inflated payments from CMS.
This case was initiated by a whistleblower: a former Aetna risk-adjustment coding auditor. That individual will receive $2 million from the settlement. The qui tam case was filed in federal court in the Eastern District of Pennsylvania.
The implication for payer CFOs is straightforward. The person who identified this pattern and brought it to DOJ was an internal coding auditor. Someone who sat inside the organization's risk adjustment function. Someone whose job included reviewing exactly the records at issue.
What the False Claims Act Actually Requires Payers to Do
The False Claims Act does not require proof that a company intended to defraud the government in the traditional criminal sense. The statute applies when an organization had "actual knowledge" of a false claim, acted with "deliberate ignorance," or showed "reckless disregard" for the truth. The distinction between those three standards matters significantly when you are building your compliance program.
Penalties under the FCA are severe. Violators can face liability for three times the government's actual damages, plus civil penalties per false claim. The statute of limitations is generally six years from the violation, or three years from when the government knew or should have known — up to a maximum of ten years.
For a payer organization, the practical translation is this: if your internal chart review process identifies inaccuracies and you do not act on them, you are potentially accumulating exposure under the deliberate ignorance or reckless disregard standards. Ignorance of what your own coders found is not a defense.
CMS receives diagnosis code data that it uses to calculate risk-adjusted payments totaling over $530 billion annually across the Medicare Advantage program. The government has made clear it intends to protect that investment. As Assistant Attorney General Brett A. Shumate stated in the settlement announcement, the DOJ will continue to hold accountable insurers that knowingly submit inaccurate or unsupported diagnoses to improperly inflate reimbursement.
This is the operating environment your compliance and finance functions must build for.
The Whistleblower Dynamic Payer CFOs Cannot Ignore
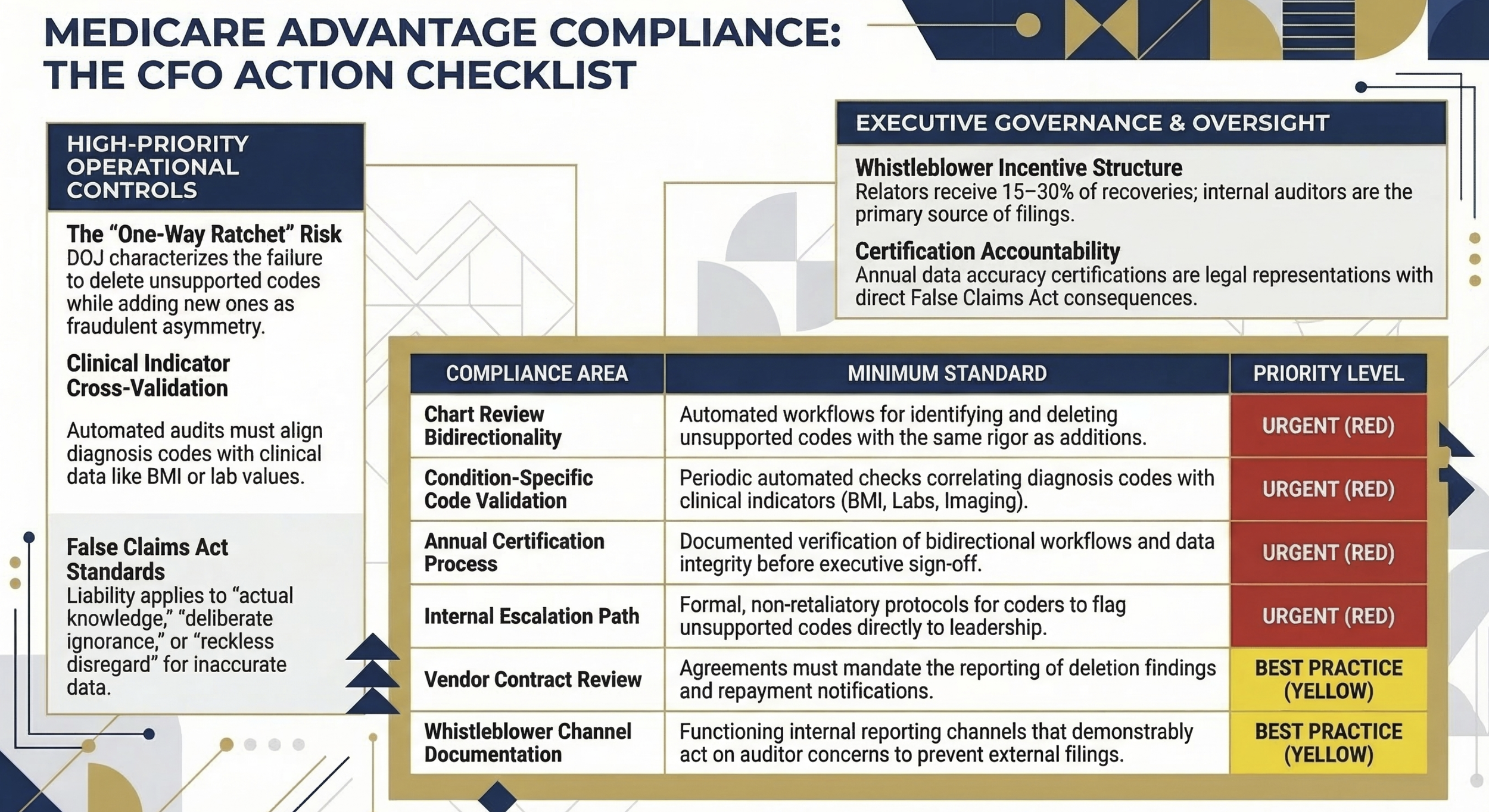
The False Claims Act's qui tam provisions allow private individuals — including current and former employees — to file lawsuits on behalf of the government when they believe false claims have been submitted. Relators (whistleblowers) can receive between 15 and 30 percent of the total amount recovered. In this case, the former Aetna auditor received $2 million.
That reward structure creates powerful incentives. Employees in your risk adjustment, coding, and compliance functions are legally protected from retaliation for reporting suspected violations, and they stand to receive a material financial benefit from doing so. The three-year retaliation statute of limitations means that a terminated coder who believed they were dismissed for raising concerns has years to file.
From my work on the payer side at Florida Blue Medicare, the coders and auditors who work directly in risk adjustment see things that senior finance leaders often do not. They see the volume of codes, the patterns across cohorts, the disconnect between what a chart says and what gets submitted. Building internal channels where those individuals can raise concerns without fear — and where those concerns are acted on — is not a compliance checkbox. It is a material risk management strategy.
In the Aetna case, the absence of that dynamic is implicit. An auditor went external. The cost was $117.7 million.
Three-column process flow showing (1) Chart Review Trigger, (2) Code Added / Code Requires Deletion fork, (3) Compliance Action Required vs. Current Aetna Pattern.
The Audit Protocols Your Organization Needs Right Now
Finance and compliance leaders at payer organizations should use this settlement as a forcing function to stress-test three specific operational areas.
Chart Review Bidirectionality
Your chart review program must be symmetrical. Every process that identifies additional codes to submit must have a corresponding, equally rigorous process for identifying and deleting unsupported codes. That deletion process needs to be documented, tracked, and reported up through finance and compliance leadership on a regular basis.
If your chart review vendor or internal team does not have a formal deletion workflow — with escalation protocols when deleted codes result in repayment obligations to CMS — that gap needs to close before your next CMS reconciliation cycle.
Condition-Specific Code Validation
The morbid obesity allegations were clinically specific. The codes submitted did not align with the recorded BMI in the member's chart. This is not a complex audit to run internally. For any condition where the diagnosis code is directly correlated with a measurable clinical indicator — BMI, lab values, imaging findings — your coding team should run periodic automated checks to confirm alignment.
CMS has the same data your coders have access to. The agency can and does run these checks on the back end. If your submission does not hold up to that analysis, you have exposure.
Annual Certification Integrity
Part of the Aetna allegation includes the charge that Aetna falsely certified in writing to CMS that its diagnosis data was accurate and truthful. That annual certification is not a formality. It is a legal representation with False Claims Act consequences if it is inaccurate.
Before your CFO or compliance officer signs that certification, there should be a documented process confirming that (1) your chart review program is bidirectional, (2) your code deletion process is functioning, and (3) the data being certified has been reviewed by someone with operational knowledge of where inaccuracies are most likely to appear.
What Payer Finance Leaders Should Bring to the Executive Table
The Aetna settlement is the second major Medicare Advantage risk adjustment case in recent months. Earlier this year I covered what Kaiser's $556M settlement teaches finance leaders about risk adjustment exposure — and the pattern is consistent. The DOJ and HHS-OIG have made Medicare Advantage risk adjustment a sustained enforcement priority.
For payer CFOs and senior finance leaders, the conversation at the executive and board level should include several specific questions.
What is our current chart review deletion rate, and how does it compare to our addition rate? A deletion rate that is significantly lower than your addition rate should prompt a documentation review. It does not necessarily indicate fraud — but it is the pattern that will draw scrutiny.
How are coding vendors contractually obligated to report deletion findings? If your vendor agreement incentivizes code additions but does not create clear obligations around deletions and repayment notifications, that contract needs to be reviewed with your legal and compliance teams.
What is our internal escalation path when a coder identifies a potentially unsupported code? If the honest answer is "there is not one," that gap is a liability.
What is our whistleblower prevention and response protocol? Prevention here does not mean suppressing legitimate concerns. It means ensuring that employees with concerns have internal channels that work, reducing the incentive to go external.
If you are a payer CFO or compliance leader building a risk adjustment audit framework — or if you are a health system CFO whose payer contracts depend on accurate risk coding from your documentation — I want to hear what you are doing differently in 2026. Hit reply and tell me where the friction points are in your current process.
Structured checklist table Content: Two-column table with "Compliance Area" and "Minimum Standard" headers. Rows: Chart Review Bidirectionality, Condition-Specific Code Validation, Vendor Contract Review, Annual Certification Process, Internal Escalation Path, Whistleblower Channel Documentation.
The Broader Enforcement Signal
The $530 billion annual MA program is not going to attract less scrutiny in 2026 and 2027. CMS continues to refine its risk adjustment data validation audit process. The OIG's work plan consistently includes Medicare Advantage diagnosis coding as a priority area. And the qui tam provisions of the False Claims Act mean that internal employees remain a persistent enforcement channel regardless of how robust government auditing becomes.
For payer organizations, this is not a moment for compliance theater. The Aetna settlement — like the Kaiser settlement before it — describes real operational processes that generated real exposure over multiple years. The corrective action required is operational, not just legal.
Finance leaders are not compliance officers. But finance leaders are signatories to certifications, owners of vendor budgets, and the executives who ultimately need to answer to boards and investors when a nine-figure settlement appears in the financial statements.
Building the operational discipline to pass a DOJ investigation is now a core component of payer financial management. The organizations that treat it as such will spend their compliance budget on prevention. The ones that do not will spend it on settlements.
What This Means for Health System Finance Leaders
A brief note for provider-side readers: the risk adjustment dynamic affects your organization too, even if you are not a payer.
If you are operating under risk-bearing contracts — capitated arrangements, shared savings programs, or full-risk Medicare Advantage partnerships — the accuracy of the diagnosis codes your clinical documentation team generates flows directly into how your payer calculates risk-adjusted payments. Inaccurate documentation on your end creates exposure for the payer, which creates downstream contract and relationship risk for you.
I covered the coding-to-reimbursement linkage in detail in my analysis of the CMS Medicaid Fraud Crackdown published earlier this month. The documentation integrity principles are the same whether you sit on the payer or provider side of the transaction.
The Bottom Line for Payer CFOs
Aetna's $117.7 million settlement is a detailed, public case study in how Medicare Advantage risk adjustment fraud is identified, investigated, and resolved. The operational failures at issue — a non-bidirectional chart review program, persistent submission of clinically unsupported codes — are correctable. They require process investment, not organizational transformation.
The cost of correction is a fraction of the cost of a settlement. The cost of a whistleblower filing is reputational and financial in ways that go beyond the settlement number itself.
Your compliance team needs the operational authority to make the chart review process symmetrical. Your finance team needs to build deletion rate reporting into its MA compliance dashboard. And your certification process needs to reflect what is actually happening in your risk adjustment function — not what you hope is happening.
The DOJ has now resolved two nine-figure Medicare Advantage risk adjustment cases in the past year. The enforcement signal could not be more direct.
Healthcare Finance Unfiltered covers the operational and financial realities that CFOs and finance leaders are navigating in real time. If this analysis was useful, subscribe for weekly coverage at rachelbarksdale.substack.com — or connect with me at hfi.consulting
P.S. When your chart review vendor delivers results, does your team run the deletions with the same rigor as the additions? Hit reply and tell me what your current process looks like — I am hearing very different answers from plans of all sizes right now.